Act now and download your Paloalto-Networks PCNSA test today! Do not waste time for the worthless Paloalto-Networks PCNSA tutorials. Download Update Paloalto-Networks Palo Alto Networks Certified Network Security Administrator exam with real questions and answers and begin to learn Paloalto-Networks PCNSA with a classic professional.
Online Paloalto-Networks PCNSA free dumps demo Below:
NEW QUESTION 1
What are two differences between an implicit dependency and an explicit dependency in App- ID? (Choose two.)
- A. An implicit dependency does not require the dependent application to be added in the security policy
- B. An implicit dependency requires the dependent application to be added in the security policy
- C. An explicit dependency does not require the dependent application to be added in the security policy
- D. An explicit dependency requires the dependent application to be added in the security policy
Answer: AD
NEW QUESTION 2
Which statement is true regarding a Prevention Posture Assessment?
- A. The Security Policy Adoption Heatmap component filters the information by device groups, serial numbers, zones, areas of architecture, and other categories
- B. It provides a set of questionnaires that help uncover security risk prevention gaps across all areas of network and security architecture
- C. It provides a percentage of adoption for each assessment area
- D. It performs over 200 security checks on Panorama/firewall for the assessment
Answer: B
NEW QUESTION 3
How many zones can an interface be assigned with a Palo Alto Networks firewall?
- A. two
- B. three
- C. four
- D. one
Answer: BC
Explanation:
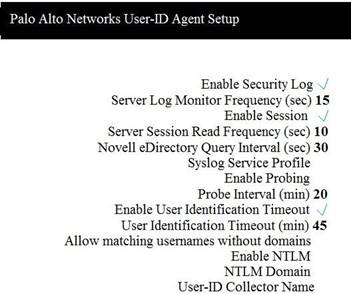 5. Which two configuration settings shown are not the default? (Choose two.)
5. Which two configuration settings shown are not the default? (Choose two.)
A. Enable Security Log
B. Server Log Monitor Frequency (sec)
C. Enable Session
D. Enable Probing
NEW QUESTION 4
Which statement is true regarding a Best Practice Assessment?
- A. The BPA tool can be run only on firewalls
- B. It provides a percentage of adoption for each assessment data
- C. The assessment, guided by an experienced sales engineer, helps determine the areas of greatest risk where you should focus prevention activities
- D. It provides a set of questionnaires that help uncover security risk prevention gaps across all areas of network and security architecture
Answer: B
NEW QUESTION 5
Based on the security policy rules shown, ssh will be allowed on which port?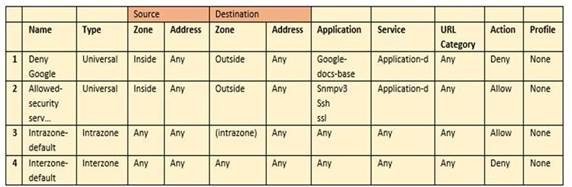
- A. 80
- B. 53
- C. 22
- D. 23
Answer: C
NEW QUESTION 6
An administrator receives a global notification for a new malware that infects hosts. The infection will result in the infected host attempting to contact a command-and-control (C2) server. Which two security profile components will detect and prevent this threat after the firewall’s signature database has been updated? (Choose two.)
- A. vulnerability protection profile applied to outbound security policies
- B. anti-spyware profile applied to outbound security policies
- C. antivirus profile applied to outbound security policies
- D. URL filtering profile applied to outbound security policies
Answer: BD
NEW QUESTION 7
Which two Palo Alto Networks security management tools provide a consolidated creation of policies, centralized management and centralized threat intelligence. (Choose two.)
- A. GlobalProtect
- B. Panorama
- C. Aperture
- D. AutoFocus
Answer: BD
NEW QUESTION 8
Which license must an Administrator acquire prior to downloading Antivirus Updates for use with the firewall?
- A. Threat Prevention License
- B. Threat Implementation License
- C. Threat Environment License
- D. Threat Protection License
Answer: A
NEW QUESTION 9
Which data-plane processor layer of the graphic shown provides uniform matching for spyware and vulnerability exploits on a Palo Alto Networks Firewall?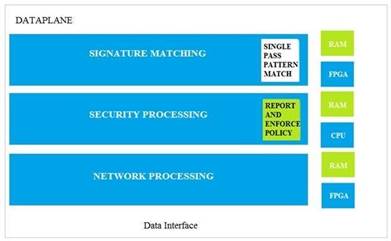
- A. Signature Matching
- B. Network Processing
- C. Security Processing
- D. Security Matching
Answer: A
NEW QUESTION 10
Which User-ID agent would be appropriate in a network with multiple WAN links, limited network bandwidth, and limited firewall management plane resources?
- A. Windows-based agent deployed on the internal network
- B. PAN-OS integrated agent deployed on the internal network
- C. Citrix terminal server deployed on the internal network
- D. Windows-based agent deployed on each of the WAN Links
Answer: A
NEW QUESTION 11
Users from the internal zone need to be allowed to Telnet into a server in the DMZ zone. Complete the security policy to ensure only Telnet is allowed.
Security Policy: Source Zone: Internal to DMZ Zone services “Application defaults”, and action = Allow
- A. Destination IP: 192.168.1.123/24
- B. Application = ‘Telnet’
- C. Log Forwarding
- D. USER-ID = ‘Allow users in Trusted’
Answer: B
NEW QUESTION 12
......
100% Valid and Newest Version PCNSA Questions & Answers shared by Dumpscollection.com, Get Full Dumps HERE: https://www.dumpscollection.net/dumps/PCNSA/ (New 115 Q&As)